Project Indeglo
Research on highly sensitive detection of unauthorized access and global warning mechanism
Detecting and preventing unauthorized access is important to ensure information security on the Internet, but fraud techniques are becoming more sophisticated day by day, and conventional individual responses have their limits. However, as networks become faster, it is impractical to comprehensively investigate the vast amount of access information, and the actual detected information is often only the "tip of the iceberg" of unauthorized access. For example, individual accesses when scanning for security holes appear to be unrelated, making it difficult to grasp the overall picture in real time. High-sensitivity detection technology that can quickly detect the slightest abnormality in its entirety is needed. On the other hand, since many unauthorized accesses use other sites as a stepping stone, there is a possibility that third parties may unwittingly facilitate unauthorized access. In order to prevent fraud, it is important to not only detect but also identify access routes. This proposal aims to build an integrated system for detecting and diagnosing unauthorized access. It features a new method for detecting minute anomalies in huge amounts of traffic, and an access route investigation function linked to route policy information. This system will realize an early warning system for unauthorized access that can detect unauthorized access on high-speed networks with high sensitivity and investigate the sender, relay, and potential scope of influence on a global Internet scale.
Invention project
Real-time detection of "traffic behavior" indicated by unauthorized access
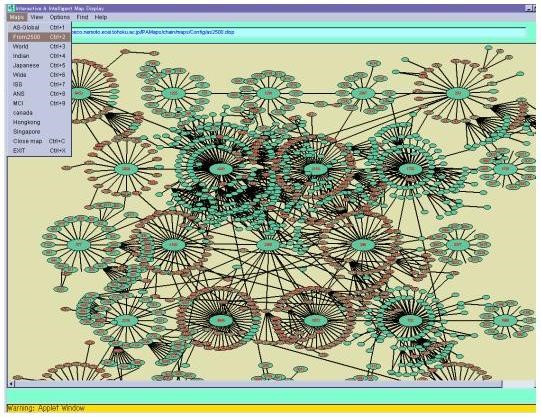
Research on how to configure and improve performance of dynamic access trees that connect information in real time
Integration and application with network maps
Research on a map-based investigation and diagnosis system that evaluates the originator, access route, and influence area of unauthorized access
Early warning system for unauthorized access and distribution method using standard format for detection results
Research on a standard method for describing unauthorized access information for rapid information exchange with sites